Command injection attacks are possible when an application passes unsafe user supplied data (forms, cookies, HTTP headers etc.) to a system shell. Commands Cheat Sheets. Related tags: Linux Line Bash Shell Vim 92 Cheat Sheets tagged with Commands. Bash (10) Cisco (9) Commander (9) Commandments (9) Networking. GNU Bash or simply Bash is a Unix shell and command language written by Brian Fox for the GNU Project as a free software replacement for the Bourne shell. Bash Cheat Sheet for UNIX Systems that might be helpful while you working on UNIX systems. Bash: Process Handling Cheat Sheet # To suspend a job, type CTRL+Z while it is running.
This table shows the other attack patterns and high level categories that are related to this attack pattern. These relationships are defined as ChildOf and ParentOf, and give insight to similar items that may exist at higher and lower levels of abstraction. In addition, relationships such as CanFollow, PeerOf, and CanAlsoBe are defined to show similar attack patterns that the user may want to explore.| Nature | Type | ID | Name |
|---|---|---|---|
| ChildOf | Standard Attack Pattern - A standard level attack pattern in CAPEC is focused on a specific methodology or technique used in an attack. It is often seen as a singular piece of a fully executed attack. A standard attack pattern is meant to provide sufficient details to understand the specific technique and how it attempts to accomplish a desired goal. A standard level attack pattern is a specific type of a more abstract meta level attack pattern. | 66 | SQL Injection |
| View Name | Top Level Categories |
|---|---|
| Domains of Attack | Software |
| Mechanisms of Attack | Inject Unexpected Items |
Command Injection vulnerabilities are a class of application security issue where an attacker can cause the application to execute an underlying operating system command. For that reason it’s generally a high impact issue. It can be exploited simply by chaining commands along with the expected input by using shell control characters such as:
Developers have a variety of reasons why they might want their web applications to execute underlying operating system commands. Apple computer programs. One example could be an application that allows a user to check if a host is online by pinging its IP address. The URL for this function could look something like this:
Safe torrenting program. and the output on the screen could be:
However if user input is insecurely passed to this function a user could chain a command on the end, such as ” && id” and this would be executed along with the main command, changing the input in our example to this:

LDAP Injection
and so the output on the screen would be:
As you might guess from above, the user gains the permissions that the affected application has, so if it’s running as www-data or root you’d get that privilege level! An easy way to compromise a box and potentially allow an attacker to take over the webserver, deface the application or steal confidential data!
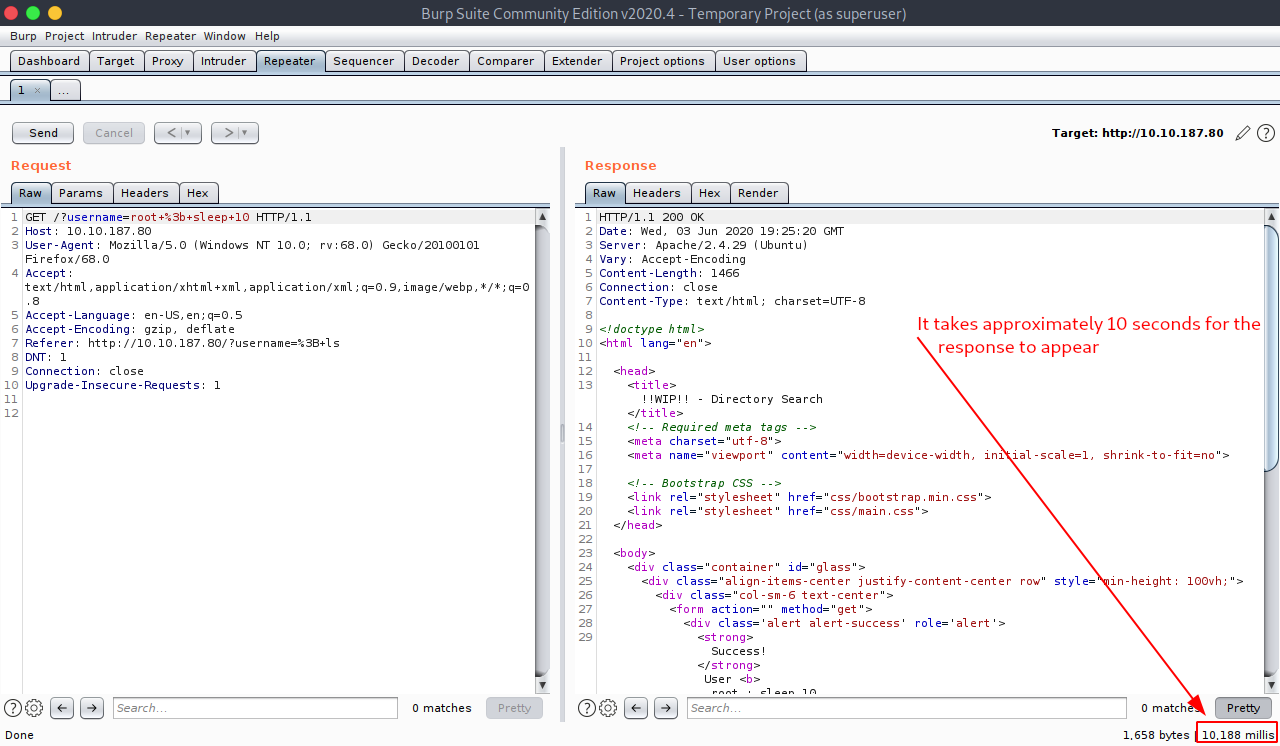
However things get more complicated for the attacker is the system does not show the output in the application itself, it might just silently execute the command and output something generic like “Success” or “done”. If this is the case an attacker can still determine the existance of the vulnerability and blindly exploit it through inference.
For example imaging chaining to the end of the input the linux command “sleep”, such as:

Bash Commands Cheat Sheet Windows

With this request the output, if vulnerable, would come through as expected with the “Success” message, however it would take a noticable about of time to return – something around 10 seconds longer than without the payload. To determine if this was just a laggy server or not you could try multiple different delay levels to see if the received delay matches the expected amount. So sleep 10 causes approximately a 10 second delay and sleep 30 causes approximately a 30 second delay, reducing the likelihood that this is a false positive.
Http://blog.php-security.org/archives/76-Holes-in-most-preg_match-filters.html
At this point you’ve got a successful Blind Command Injection vulnerability! Before I get on to how to utilise that as an attacker however, there’s one more type to deal with. Free antivirus for windows xp. Blind injection with out-of-band detection. This class occurs is a vulnerability is vulnerable but no change in output can be perceived through the application, for example if the application executes the request in a new thread, so delaying the server through the “sleep” command doesn’t work (or at least can’t be perceived through the application itself).
In this case we can get our “noticable change” by calling out to another server and monitoring that server for requests. For example you could try a payload like the following:
CWE-78: OS CommandInjection
This would cause an affected (Linux) server to call out to the attacker’s machine. The wget command online requests the server download a web page. Therefore the attacker could see that the payload worked successfully as their logs would show a GET request to the file: /?attacksuccessful
Now to turn that into a viable attack payload to, for example, steal confidential files the attacker could try chaining the contents of the file in the request to the attackers server! A payload like this would be effective:
Here the attacker is taking the contents of the confidential file /etc/password, encoding it with base64 so that it’s possible to transmit it in a URL and then using the wget command again to send that file in a HTTP GET request to the atttacker controlled server! One thing to remember is that the base64 command will line wrap by default after 76 characters, but you can use -w 0 parameter to disable this, like this:

As you can imagine, this is a pretty bad vulnerability which I’ve seen multiple times during Penetration Testing engagements but I’ve seen little in the way of content online about the issue, so I thought I’d throw a few notes down in a post. The important part though: there are specific ways to secure command execution depending on your underlying language and programming framework however one thing that’ll work for general cases is effective user input filtering! Luckily, I’ve written about that here!
Again, the minimum characters to consider dangerous in regards to this issue are:
Payloads can be incredibly varied as the attacker has an awful lot of flexibility, but a few simple ones are things like:
